 In often cases software companies or independent developers distribute the binary files of their software using sources different than the original website. This creates a risk of making the original binaries corrupted, making the computer used to download them corrupt.
In often cases software companies or independent developers distribute the binary files of their software using sources different than the original website. This creates a risk of making the original binaries corrupted, making the computer used to download them corrupt.
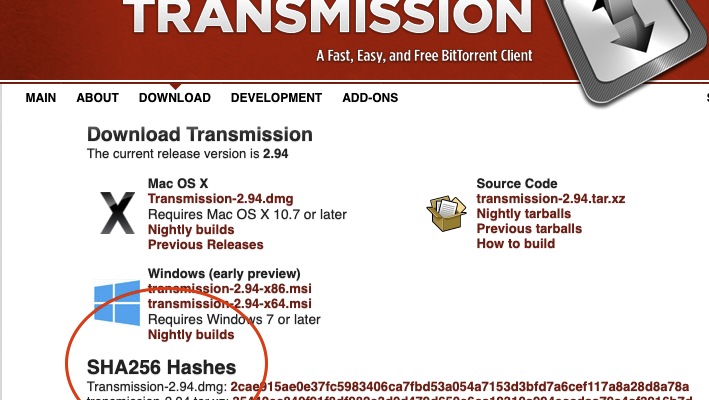
For instance, versions of popular programs (e.g., BitTorrent clients) corrupted and disseminated by hackers include malware that turns the victims’ computer into so-called bots, injects spyware and ads or even mine Bitcoins, thus generating profit for the hackers.
Trying to reduce this risk, developers use a cryptographic check-sum or hash, corresponding to the binary file of their program. The functions used to generate such check-sums are built in a way that it is not tractable to generate another file with the exact same check-sum. Therefore, if the binary file of a program is corrupted, the corresponding hash will be different from that of the original file, thus allowing the users who download it to detect the corruption and cancel its installation.
Project Leader: Kévin Huguenin.
UNIL collaborators: Bertil Chapuis.
External collaborators: Alexandre Meylan (Kudelski Security), Mathias Humbert (Armasuisse), Igor Bilogrevic (Google).
Publications
- A. Meylan, M. Cherubini, B. Chapuis, M. Humbert, I. Bilogrevic, and K. Huguenin. 2020. A Study on the Use of Checksums for Integrity Verification of Web Downloads. ACM Transasctions on Privacy and Security (TOPS), 24, 1, Article 4 (September 2020), 36 pages. DOI: 10.1145/3410154
- B. Chapuis, O. Omolola, M. Cherubini, M. Humbert, K. Huguenin. An Empirical Study of the Use of Integrity Verification Mechanisms for Web Subresources. In Proc. of the The Web Conference (WWW’20), Taipei, Taiwan, Apr 2020. DOI:10.1145/3366423.3380092
- M. Cherubini, A. Meylan, B. Chapuis, M. Humbert, I. Bilogrevic, K. Huguenin (2018). Towards Usable Checksums: Automating the Integrity Verification of Web Downloads for the Masses. In Proc. of the 25th ACM Conference on Computer and Communications Security (CCS’18), Toronto, ON, Canada, Oct 2018. DOI: 10.1145/3243734.3243746